Error62
Current Vulnerability Status
The Terrestrial Internet is Compromised.
Software alone cannot stop a physical breach.
IT networks and standard chips are compromised.
Cables can be cut. Local networks suffer from cyber attacks. IP addresses are spoofed.
Financial entities are legally mandated to physically fortify their IT infrastructure.
We are the hardware solution.
WE PROTECT CRITICAL DATA
SYSTEM ALERT
> IP SPOOFING DETECTED
> FIREWALL BYPASSED
> CABLE COMPROMISED
> HIJACKING IN PROGRESS
We do not fix the internet we bypass it entirely.
65,535 ways to attack you
65,535 Doors.
One Perimeter.
A standard router exposes up to 65,535 TCP and UDP ports.
Attackers only need to exploit one weakness.
You must secure every entry point continuously.


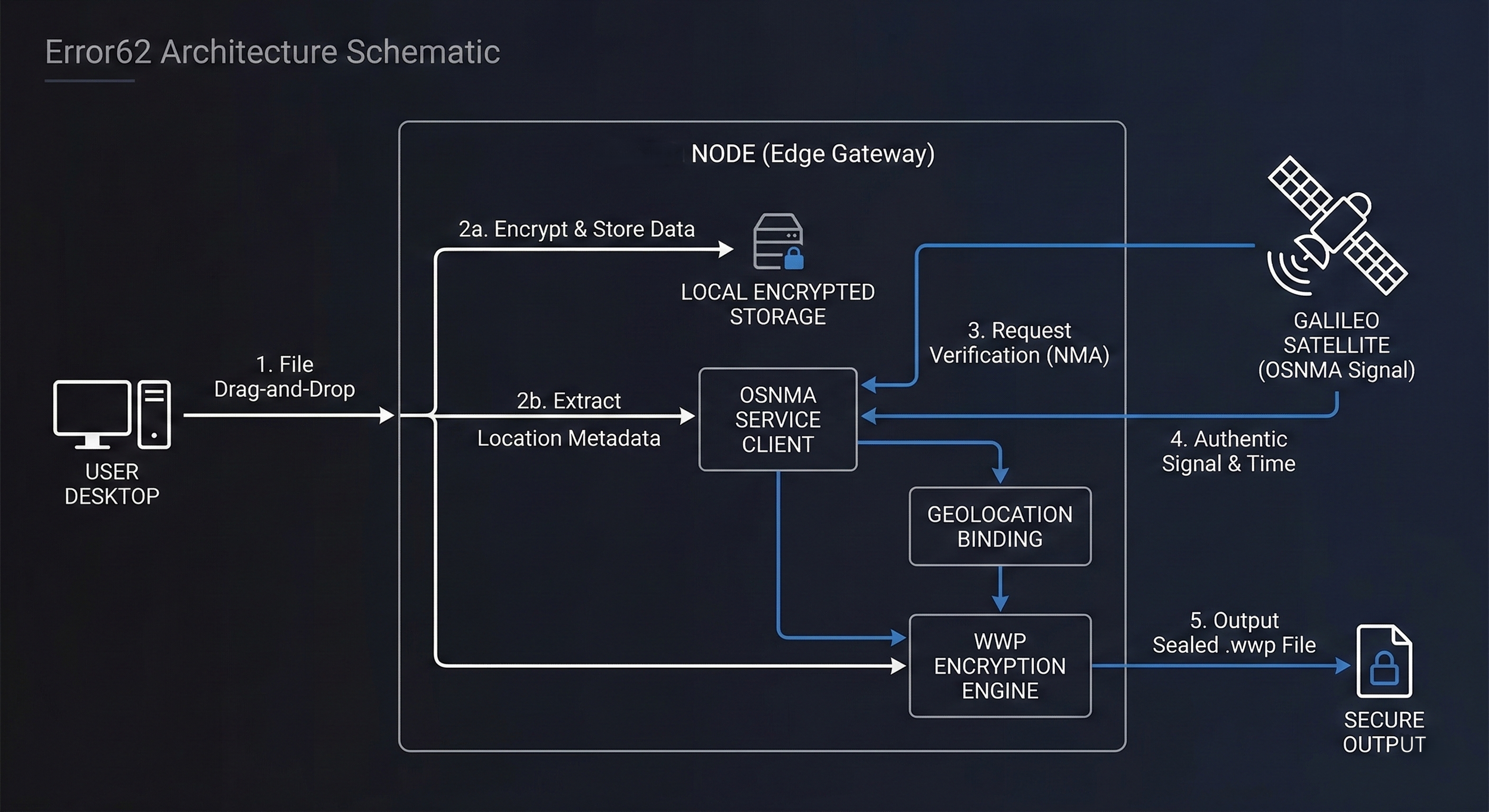
The Architecture of our Defense
We do not rely on digital trust; we rely on physics.
The Triton Edge-Node physically
binds your sensitive enterprise data to a specific geographic coordinate using satellite signatures.
If a attacker attempts to exfiltrate
the data outside of your physical perimeter, your file will permanently locks.
Files are encrypted into envelopes that cannot be decrypted outside the authorized physical perimeter.
The cryptographic flow:
Zero Operational Friction.
When security protocols are too complex, employees find ways to bypass them.
The Triton Vault solves this by operating entirely
out-of-band and in the background.
It requires zero employee training, zero additional passwords, and
zero workflow
disruption.
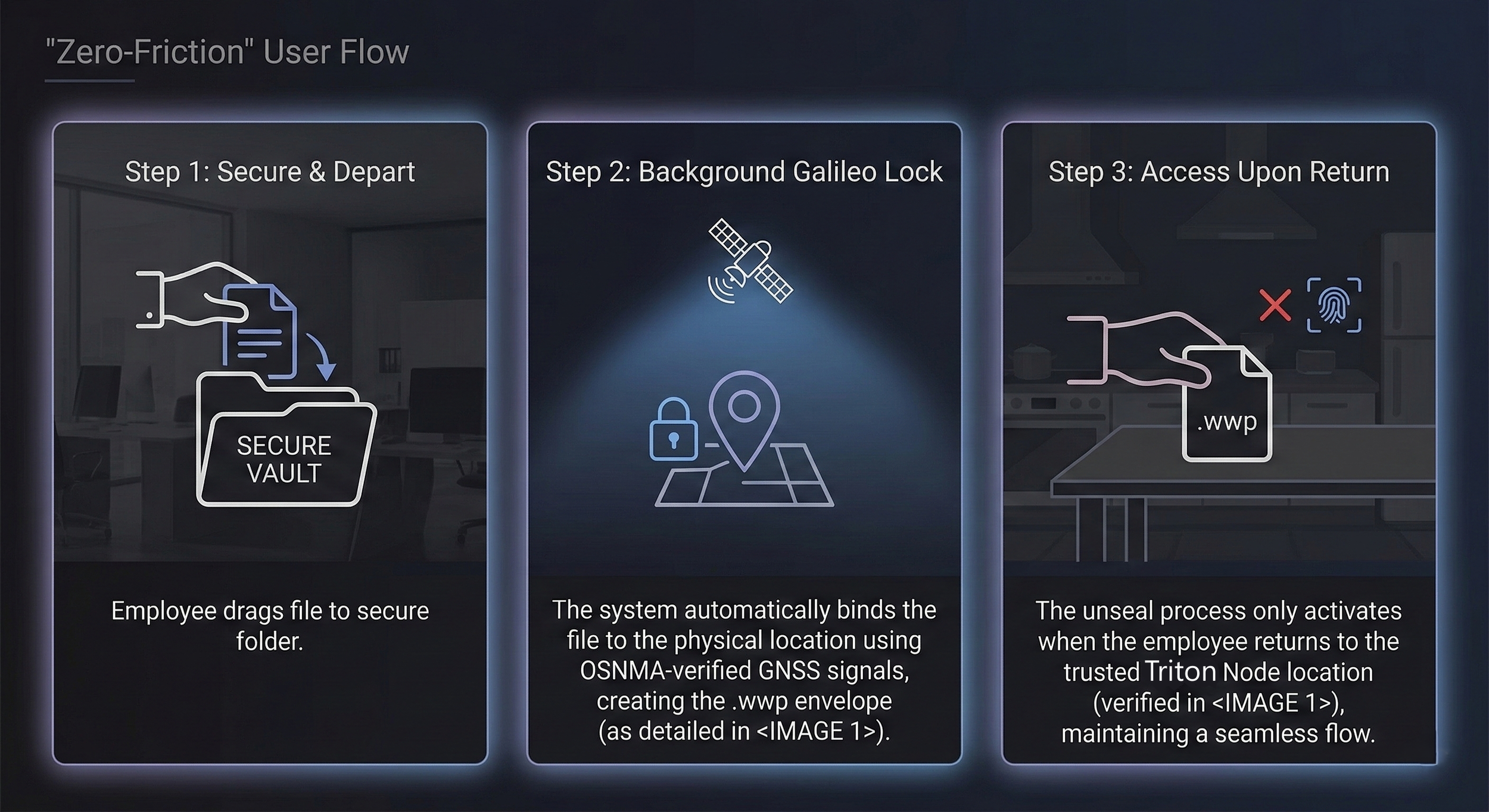
Total Compliance. Total Invisibility.
You achieve mandatory DORA physical resilience without retraining a single
employee. The attackers cannot spoof the physical satellite signature, and your
workforce doesn't even know the vault is there.
Deployable Physical Resilience.
We engineered Triton to survive both digital and physical siege.
This is not a standard commercial router; it is a
decentralized cryptographic fortress.
Operating at an ultra-low 15W power draw, the Triton node is fully compatible with off-grid solar arrays and solid-state battery.
Modular Defense Architecture
Internal Payload:
Fully Customizable
Whether you require extended solid-state battery arrays for grid-independent, or enhanced edge-compute for massive file volumes, we tailor the internal hardware to your exact enterprise needs.
Active Perimeter:
Deterrence Software cannot s****m when breached;
Triton can. Choose from 3 rapid-deployment base models, or commission a custom-scaled node for sovereign data centers.
You are Either Physically Secure, or You are Waiting to be Breached.
The attackers are already scanning your network.
Close the terrestrial door before they find it.

